● To compete in today’s fast-paced competitive environment, organizationsarincreasinglyall
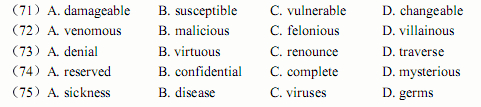
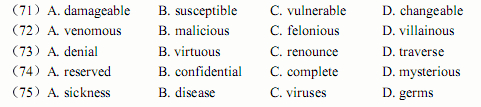
● To compete in today’s fast-paced competitive environment, organizations arincreasinglyallowing contractors, partners, visitors andgueststoaccesstheirinternalenterprisnetworks.Theseusersmayconnect to the network through wired ports in conference rooms ooffices, or via wireless accesspoints.Inallowing this open access for third parties, LANs becom(71).Third parties can introduce risk in a variety of ways from connecting with an infectelaptop to unauthorized access of network resources to (72)activity. For many organizationhowever, the operational complexity and costs to ensure safe third party network access havbeen prohibitive. Fifty-two percent of surveyed CISOs state that they currently use a moat ancastle’s security approach, and admit that defenses inside the perimeter are weak. Threats fromnternal users are also increasingly a cause for security concerns. Employees with maliciouintent can launch (73)of service attacks or steal (74)information by snooping thnetwork. As they access the corporate network, mobile and remote users inadvertently can infethe network with (75)and worms acquired from unprotected public networks. Hackemasquerading as internal users can take advantage of weak internal security to gain access tconfidential information.
 题目内容
(请给出正确答案)
题目内容
(请给出正确答案)

 如搜索结果不匹配,请
如搜索结果不匹配,请